Monday, December 03, 2007
Your Christmas Present: Useful Free Software!
CobianBackup is a Windows backup of a different breed - I'll be blogging on this gem more, I'm sure. It can compress and encrypt your information, so it' s HIPAA compliant!
Wednesday, November 07, 2007
Using CrossLoop to Get Help
I found this utility for fast and easy Windows desktop sharing called Crossloop. This program is very easy to install, and oh yeah, it's supposed to be secure, too.
Any time you need to help out a friend or coworker, use this tool - it will save a lot of time and headache! Watch the video above to get started.
If you get a Windows Firewall warning, click Always Allow.
If you get a Windows Defender warning, click Review, then, under the action column, select Always Allow.
Tuesday, November 06, 2007
Medicare Part A Submission (EDI) - Revisited
What's new? Just the way that you connect to the AT&T Global Network. If you have an high-speed Internet connection, you now have the option of using a VPN (Virtual Private Network) to connect. What does this mean? Well, you don't need a modem. And it's faster. Much faster.
So how do you get it? First, call IVANS and request a new VPN account - your current dial-up username and password won't work. They will fax you a form to fill out and fax back. three to five days later, they will fax or mail a confirmation message. Once you have received this, go to the IVANS Download Page and find the column that best describes your operating system. If you're not sure, find My Computer, right-click on it, and select Properties. What will come up is a window describing your computer, and the info in the upper-right area is what is most important as it will say Windows 98 or 2000 or XP or whatever. Pick the VPN Access software appropriate for your computer, download it and save it someplace safe. Next, download and print out the VPN Enabling Guide that is appropriate for your computer - it is a must-read for making this go. Don't worry, they make it easy!
Warning, one major irritation is the included Firewall. I think it's nice of them to want to protect us from evil hackers and all, but it can cause some headaches. Like making your computers shared files and printers unavailable to your coworkers. So after you have finished with the instructions you have printed out, make sure and click Start -> Programs -> AT&T Global Network -> AT&T Firewall, then click Off. Save this setting and you're ready to rock!
Thursday, October 25, 2007
I Hate HP All-In-One Printers
For the last 6 years, HP has produced multifunction Printer/Scanners/Copiers (PSC's) and PSC's with Fax (All-In-One, or, AIO). Seldom has Windows happily accepted the software then continued to work well without a hiccup. Most typically, just getting Windows to load the software has been enough to make me want a beer. And a hammer. Just a few days ago, I went to set up a AIO expecting it to take under an hour. Four hours later, I had found a solution. It wasn't easy, but once I completed these instructions, I was able to set up the printer and make it work as expected.
This shouldn't be necessary, and is enough to make me say I hate HP All-In-One's,but, they still look good on a desk.
Tuesday, October 16, 2007
Taking Screenshots is OS X
| Key Combination | Result |
|---|---|
| Command+Shift+3 | Capture entire screen and save as a file |
| Command+Control+Shift+3 | Capture entire screen and copy to the clipboard |
| Command+Shift+4 | Capture dragged area and save as a file |
| Command+Control+Shift+4 | Capture dragged area and copy to the clipboard |
| Command+Shift+4 then Space bar | Capture a window, menu, desktop icon, or the menu bar and save as a file |
| Command+Control+Shift+4 then Space bar | Capture a window, menu, desktop icon, or the menu bar and copy to the clipboard |
(This is from MacDevCenter)
Saturday, October 06, 2007
Tools that make my geeky life easier:
My favorites?
Well, I like NTBackup Print Log because it does that: watches for NTBackup to finish, then finds the last log file and sends it to a printer. This helps supply some of NTBackup's missing functionality (however, I need a utility that helps make scheduling simpler and one that adds support for pre/post-backup commands).
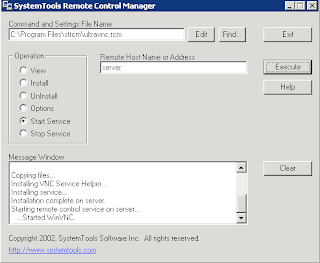
The other indispensable tool is the frighteningly effective Ultra VNC Pusher which can push VNC into a remote Windows computer to which you have SMB access. Not for the faint of heart!
Wednesday, September 05, 2007
New MDS/OASIS VPN Connection Available
Apparently our friends as CMS forgot that we are all highly dependent on our computer networks and that we occasionally keep important stuff like MDS files on a network drive. So when we connect to MDS/OASIS using the VPN and try to upload our MDS's from a network drive thenetwork drive is unreachable and we cannot select and submit our files.
I did what any good tech does before pulling his hair out - I called tech support. The guy at CMS tech support was friendly and knowledgeable, and acknowledged that this is a problem. Furthermore, the tech assured me that this is by design. Apparently the rest of our network presents a threat to CMS's computers (I'm paraphrasing here), so the machines that connect to CMS are quarantined from their network.
The tech went on to explain that CMS expects users with networked computers to copy MDS's from the network to their computer prior to connecting to the MDS/OASIS site.
Instead of manually copying these files, I created a batch file to copy them automatically and then launch the AT&T Global Network Client once the copy has completed. Here's how you can make your own:
- Create a text file on your desktop and rename it to a batch file by changing its filename extension to .bat - I named mine MDS-OASIS.bat
xcopy m:\marktech\XFEROUT\*.mds c:\XFEROUT /d /v /y /i
"C:\Program Files\AT&T Global Network Client\netclient.exe"
exit
- There a LINE BREAK (in other words, press Return) at then end of each line if you're typing this.
- Save this file as a .txt file and rename it as a .bat file. If you don't know how to do this, consult a computing professional.
- When you run it, a DOS window will open, it will copy all .MDS files that you don't already have to the folder c:\XFEROUT, then invoke the AT&T Global Dialer.
- When you finish your transfer and close the dialer, the DOS window will disappear.
/d only replaces files that are newer than ones on the target drive
/v verifies that each file is copied correctly
/y suppresses prompting to overwrite files on the destination computer
/i causes xcopy to assume that c:\XFEROUT is a directory, not a file.
Wednesday, August 29, 2007
Let's Waste some Time!
Joost.com has a Beta program that works on both Windows and Mac that allows you to watch TV on demand. Now we're not talking live TV here, we're talking a list of channels, each with a list of already-run shows.
 So, if you missed a few episodes, this may be the place to find them. There's MTV, Cartoon Network, WB, Indy 500, NHL, BET, and a Sports Illustrated Swimsuit channel! Myself, I've been catching up on Metalocalypse.
So, if you missed a few episodes, this may be the place to find them. There's MTV, Cartoon Network, WB, Indy 500, NHL, BET, and a Sports Illustrated Swimsuit channel! Myself, I've been catching up on Metalocalypse.Now, if you want original, more current content, check out Miro, an application which is best described as RSS [RSS defined]for video - it can be pointed at video blogs (called channels in Miro), and it will automatically download the videos whenever updates appear.
 I love the science and how-to stuff, expecially from Make magazine. Since this can reach out and get whatever you can find online, it is a very powerful tool - it can search Google, YouTube, and other video sources. Furthermore, it downloads and saves those videos, which allows them to be transferred to an iPod, shared with friends, or just saved for later. This program keps me thoroughly entertained when I dn't have an Internet connection because it downloads whatever you desire then saves it for later!
I love the science and how-to stuff, expecially from Make magazine. Since this can reach out and get whatever you can find online, it is a very powerful tool - it can search Google, YouTube, and other video sources. Furthermore, it downloads and saves those videos, which allows them to be transferred to an iPod, shared with friends, or just saved for later. This program keps me thoroughly entertained when I dn't have an Internet connection because it downloads whatever you desire then saves it for later!
Tuesday, July 17, 2007
Secure Windows Remote Desktop - Part 2, Clients

Now get Putty.exe for you client computer from HERE and run it.
Fill in your IPCop's host name or public IP and then change the port to 222.
Next, expand Connection, then SSH and select Tunnels.
Add a new forwarded port source 3399 (since this one isn't commonly used) and forward it to the target server's internal IP (NOT the IPCop's IP!) and add a :3389 to the end of the string as in the second figure.
Go back to Session, click Save, and give this
 connection a name. Click Open, and you will be prompted for a username and password - give these (preferably the remote user we created earlier instead of the dangerous root user) and you will get a prompt. You're done with Putty for now!
connection a name. Click Open, and you will be prompted for a username and password - give these (preferably the remote user we created earlier instead of the dangerous root user) and you will get a prompt. You're done with Putty for now!Now go to Start, Run, and type mstsc.
Fill in the Server line with localhost:3399 and hit connect. If all been done correctly, you will get a remote desktop on your target machine.

Secure Windows Remote Desktop - Part 1, Servers
Some background: Microsoft RDP (Remote Desktop Protocol) has vulnerabilities with regards to security and encryption (details are beyond the scope of this post). If we use a protocol that is more secure (namely SSH), then tunnel RDP through the more secure protocol, we wind up with a much more secure implementation.
Requirements:
- IPCop Firewall - or your favorite Linux distro server serving up SSH on a public IP address - I'll only address IPCop, but this can be generally applied.
- Remote Desktop Server (Like Windows XP Pro or Windows Server 2003 - other protocols like VNC will work with this, you just ned to know the required ports to fill in on your Putty Tunnel settings.
- A Windows client with Putty installed (it's easy, just go here -- and download putty.exe)
SSH to your IPCop as root and sign in.
Create a new user called remote as a member of a new group (also named remote) and use this user for shared remote access. As root, issue the following commands to add the new user:
groupadd remote
useradd -s /bin/bash -g remote -m -k /dev/null remote
The meaning of the command line options (from ifs.vlsm.org):
- -s /bin/bash
-
This makes bash the default shell for user lfs.
- -g remote
-
This option adds user remote to group remote.
- -m
-
This creates a home directory for remote.
- -k /dev/null
-
This parameter prevents possible copying of files from a skeleton directory (default is /etc/skel) by changing the input location to the special null device.
- remote
-
This is the actual name for the created group and user.
To log in as remote (as opposed to switching to user remote when logged in as root, which does not require the remote user to have a password), give remote a password:
passwd remote
Friday, April 13, 2007
Windows XP On an Intel-Based Apple (You're off to Boot Camp, Soldier!
You CAN use an earlier XP full installation CD (I've read that the upgrade can work too, but I haven't played with it) - If (that's a big if) you have an XP CD, a CD Burner, a running Windows XP Machine that can use the burner, - and some time on your hands, check out http://www.applematters.com/index.php/section/comments/how-to-the-curmudgeons-guide-to-boot-camp/, which has links to sites that tell you how to "slipstream" your SP2 and create an XP install CD with SP2.
So how well does it work? Well, ALMOST as well as Windows XP on any PC I've used - I don't know if its a portender of things to come, or just my rotten luck, but I already had a scare where the system wouldn't boot to XP this morning, and I just installed it yesterday! Luckily, after turning it off (it wouldn't respond to key presses), then letting a Scandisk run (it happened automatically because of the "bad shutdown") and fix a single problem (don't remember what it was), it booted fine, and Stan and I had a fight to the death on CnC3, he on his PC, and me on my newly Windows Mac.
Tuesday, March 27, 2007
Broken Windows Services?
I've successfully used it to fix some nagging problems with Windows Update like the lack of a crawling green progress bar and even update errors. This can also reset your Winsock (Hello LSP Fix!)
Monday, February 19, 2007
Windows Vista: Not Welcome in Nursing Homes
To: IVANS Customers Using AT&T Global Network Client
From: Paul Tuten, Director, Product Management
Re: T&T GNC Support of VistaThe current versions (5.x.x, 6.x.x) of the AT&T Global Networki Clients are not supported by IVANS/AT&T on Microsoft's new Windows Vista operating system. As such, IVANS does not recommend that you upgrade to the new operating system if you use the GNC until AT&T has released a version that supports the operating system.
AT&T plans to release a new version, 7.0 of the AT&T Global Network Client at the end of the 2nd quarter of 2007, which will provide limited support of the Windows Vista operating system. The specific limitations with 7.0 are that the following features will not be avaialble/will not work in Windows Vista:
- Managed Personal Firewall
- Network Logon Extensions (GINA or PLAP)
- 64-bit operating systems
IVANS will post the General Available (GA) release of AT&T Global Network Client 7.0 to our website www.ivans.com/downloads when available.
If you are required to migrate to the new operating system before the General Available (GA) release of 7.0 version of the client, we may have a workaround for you. Please contact our helpdesk at 1-800-548-2675 to discuss your options.
Tuesday, February 06, 2007
Vista Listens Real Good (Hack, Hack)
Someone apparantly asked the question, can "Vista listen to itself?" and the answer is apparantly, "yes." An intrepid hacker, er, erhem, I'm sorry, "Security Researcher," recorded himself issuing voice commands to his Vista computer, then played them back on his Vista PC - lo and behold, it took only minor tweaking to get it to work, including Vista opening a command prompt, and visiting a web site - uh oh, better turn off the voice command if you're using a sensitive machine.
Monday, February 05, 2007
Windows Vista Editions
- It requires too much horsepower. If your computer is less than 2 years old, then you should be fine. The BIOS dates on my three desktop PC's are: 2003 (2.4G Intel laptop currently running SUSE Enterprise Desktop 10.1 and XP Pro), 2002 (1.8G desktop currently running OpenSUSE 10.0), and 1999 (750 MHz PIII desktop running XP Pro) - I'm pretty happy with all three's performance and can't see a reason to upgrade . However, a Macbook Pro 2.16G is about to join my herd, and I will be buying a copy of Vista Ultimate to go on it.
- Currently no software that runs exclusively on Vista, and many current softwares (like iTunes) may have problems on Vista.
- It's too new. Like any OS, the best time to get it is after the 1st service pack comes out.
- No free stuff and no MS Mega-Promotions, just saw a totally disappointing interview of Bill Gates by John Stewart on the Daily Show, after which, Bill hustled out, not sitting and chatting like typical guests. When XP came out, I got as a premium for running out and buying XP on its release day: a 256MB DIMM, an MP3 player, and a cool mouse pad. What gives this time around?
Wednesday, January 31, 2007
Sharing a single XP Pro computer among several users
So what if you're part of a domain? Most of my business customers fit into this category, and as much as I hate to say it, it'll cost you some money to do it right ($550.00). Doing it wrong is indeed free - XP Unlimited offers the Enterprise version of the software, which has a free demo that is not crippled and never expires.
Using either of these tools allows two or more people to simultaneously use the same computer under different usernames, with one local user, and an unknown number of remote users - I've had as many as two remote and one local working at once with no serious degradation to performance on a fairly new Dell with a Celeron 2.8G CPU and 512MB of RAM.
This is extremely useful for organizations that can only afford one XP machine and would like to keep on using their clunkers like Windows 95 and 98 (which is unsafe at best due to viruses). Even more useful is using old computers with an open source desktop OS like OpenSUSE or another flavor of Linux and the rdesktop command - then a user on a crummy old computer that used to run Windows 9x can now use a reasonably secure, modern OS on their desktop and still have access to an XP computer to work in their preferred environment or to use applications that only work on Windows.
Tuesday, January 30, 2007
Geek Speak: Networking
The first 1024 ports have been reserved for "well-known services." The rest are generally up for grabs, although most popular programs use well-known upper port numbers - for instance, Windows Remote Desktop typically uses port 3389, but can be told to use any port through a simple registry hack.
"Listening" ports (open ports) indicate that a computer is providing a service on the network - thus "listening" for a connection. While not all network services are bad, and many are required for the proper operation of home and business networks, having a port listening on the Internet is really bad if it is unintentional - the services listening on the open ports may be exploited by worms or malicious hackers.
Server - Any computer offering services on a network is called a server by us geeks. However, a server to you office pros is the central computer that holds all your goodies while you're not working on them. For my typical customer, an office server not only stores and backs up files, but also serves the "Intranet" e-mail, calendar, and other, more essential services like authorization, authentication, and event logging.
TCP/IP - Transmission Control Protocol/Internet Protocol is a suite of networking protocols (languages) upon which the Internet, and more recently our office networks, heavily rely. It doesn't matter if you're running Windows, Linux, or Mac OS X, if you use the Internet, you use TCP/IP. When you "ping" someone, you are using the most basic parts of the TCP/IP protocol.
Wednesday, January 24, 2007
Medicare Part A Submission (EDI)
Today, most of the work is done by entities like Adminastar Federal, who are contracted with the CMS to provide service to a specific region - Administar, for instance, is in charge of the Midwest, particularly Illinois, Indiana, Kentucky and Ohio.
There are two ways that nursing homes typically submit their claims - either via batch, or via DDE (direct data entry). Most typically the people that handle the claims dial into a regional point-of-presence (POP) using theAT&T Global Dialer and use a terminal program like Microsoft's Hyperterminal, orMedacomm. Batch submittals and real-time benefits verification are typically obtained from the CMS using PC Ace Pro32 (the IVANS software for Medicare Part A verification and submission) or Passport IP - AT&T Global Dialer and Passport IP can be found at http://www.ivans.com/downloads/.
Signing up for these services is simple, and the necessary forms can be found on the CMS's web site .
Tuesday, January 16, 2007
Geek Speek Primer Series - Hard Disk Fragmentation
So for the next few entries, I will try to bring some of the more technical terms I may use to the table and discuss them in more detail.
Here Goes!
defrag - DOS and Windows command that invokes the process of defragmentation.
defragmentation - (or defragging) is a process that reduces the amount of fragmentation in file systems. It does this by physically reorganizing the contents of the disk in order to store the pieces of each file close together and in order (contiguously). It also attempts to create larger regions of free space using compaction to impede the return of fragmentation. (from Wikipedia)
file system fragmentation, sometimes called file system aging, is the inability of a file system to lay out related data sequentially (contiguously), an inherent phenomenon in storage-backed file systems that allow in-place modification of their contents. It is a special case of data fragmentation. File system fragmentation introduces disk head seeks, which are known to hinder throughput. (from Wikipedia)
malware - malicious software is software designed to infiltrate or damage a computer system without the owner's informed consent. It is a portmanteau of the words "malicious" and "software". The expression is a general term used by computer professionals to mean a variety of forms of hostile, intrusive, or annoying software or program code. (from Wikipedia)
page file - a file on your hard drive that emulates your computers random access memory (RAM - often the smallest of the vertical chips sticking up from the main computer board inside your tower or CPU). Items in memory that aren't used very often are written to the page file in order to free up space in the much faster RAM. The page file can also act as additional RAM once all of your physical RAM is in use. Since the page file is on the hard disk, transfer into and out of the page file is limited by the speed at which your hard disk operates. Hard disks rely on relatively slow mechanical systems to read and write information, dealing with memory paged to the hard disk is substantially slower than working with memory in the RAM chips. This is why the computer slows down when it is out of physical memory - it must instead perform tremendous amounts of reads and writes on the hard drive that it uses for its memory.
Tuesday, January 09, 2007
Defragment your Page File (and other Amazing Windows Feats!)
Take PageDefrag for instance - this tool lets you defragment your page file, your event logs, and your registry. While this isn't necessary in Windows XP (the built-in defrag program does this well), Windows 2000 didn't include this functionality.
Also useful is Diskmon - this tool monitors access to the hard drive, either giving detailed info, or, in the case you don't have a working hard drive light, this will put a hard drive light in the task tray.
This page has an excellent array of utilities for managing system processes and threads - including apps to list processes, and a program to KILL windows applications - good against stubborn viruses.
Autoruns is an application that lists all of the programs that start up automatically when you turn on your computer. This is handy in removing spyware or other undesirable startup programs.